This weekend I finally came around to create OpenEmbedded recipes for WireGuard. The recipe currently awaits review and hopefully will get part of the meta-networking layer, part of the meta-openembedded repository of the upstream OpenEmbedded project. There are two recipes, one for the kernel module and one for the user space tools. The user space tools have the kernel module as a dependency, hence it is sufficient to install the wireguard-tools package, e.g. by using IMAGE_INSTALL_append in your local.conf:
IMAGE_INSTALL_append = " wireguard-tools"
The kernel module needs at least a kernel version 3.18 or later and has some requirements regarding kernel configuration. The WireGuard website maintains a list of kernel requirements. If you are using the Yocto kernel, the netfilter kernel feature (features/netfilter/netfilter.scc) is enabled by default and seems to be sufficient to run WireGuard. To get started with WireGuard, refer to the excellent Quick Start guide on wireguard.io.
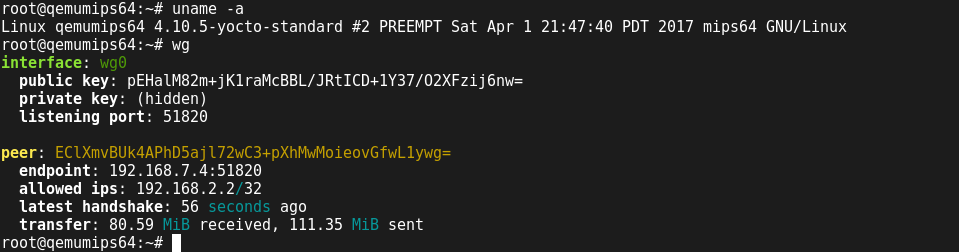
I successfully compiled a core-image-minimal with WireGuard for the two machines qemumips64 and qemuarm, and brought up a VPN connection using bridged tap devices.
$ runqemu qemuarm nographic ... $ runqemu qemumips64 nographic ... $ sudo su # ip addr flush dev tap0 # ip addr flush dev tap1 # ip link add br0 type bridge # ip link set tap0 master br0 # ip link set tap1 master br0
After setting up the VPN, iperf3 measured around 65Mbits/sec to 85MBit/sec throughput depending on direction. Not too bad considering that this were two fully emulated systems where Linux boots take between 20-30 seconds).
Hi,
I’m trying to include WireGuard in my Yocto project and I’m interested in using your recipe for that. What is the status of it? Do you need some help in testing or even developing it?
I’m just learning Yocto/BitBake/OpenEmbedded, but I think we can make it work together.
[]s
Thanks.
The recipe is in upstream meta-networking:
http://cgit.openembedded.org/meta-openembedded/tree/meta-networking/recipes-kernel/wireguard